
-
30 Jul

-
25 Jul

Are NFL games rigged?
After diving deep into the topic of whether NFL games are rigged or not, I've found that opinions are heavily divided. Some fans adamantly believe in manipulation due to controversial calls and uncanny comebacks, while others staunchly uphold the integrity of the game. Many of these conspiracy theories lack substantial proof, and the NFL consistently denies such allegations. However, it's essential to acknowledge that referees can make mistakes, but it doesn't necessarily mean the game is fixed. In conclusion, while it can be fun to speculate, there's no concrete evidence to suggest NFL games are rigged. -
23 Jul
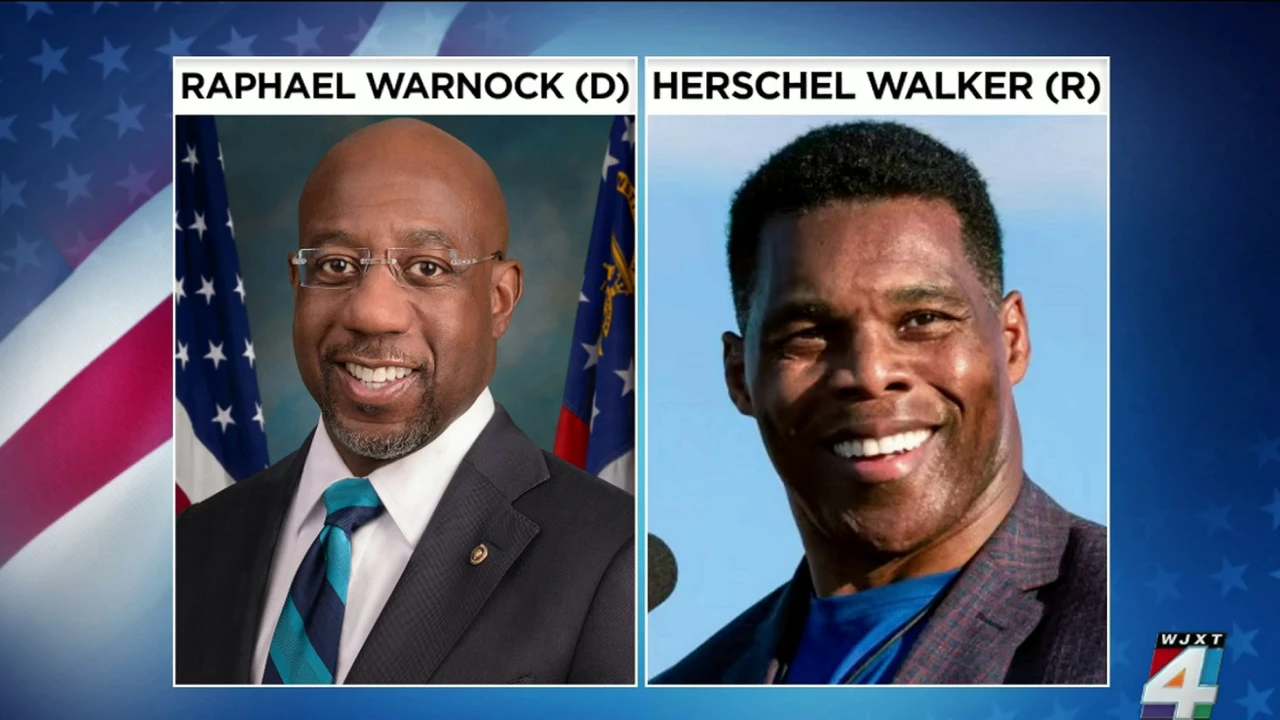
Who will win Georgia, Raphael Warnock or Herschel Walker?
It's anyone's game right now in Georgia's Senate race between Raphael Warnock and Herschel Walker. Both candidates are vying for the populaces' favor, with Warnock relying on his track record and Walker leveraging his sports fame. The outcome is uncertain and it's shaping up to be a tightly contested race. The decision will likely hinge on voter turnout and the current political climate. It's one to watch, folks, as Georgia's choice could sway the balance of power in the Senate. -
18 Jul

What sports teams have black and orange team colors?
In my exploration of sports teams rocking the black and orange colors, several names popped up. The San Francisco Giants and Baltimore Orioles of Major League Baseball both proudly sport these colors. In the National Hockey League, the Philadelphia Flyers also wear black and orange. Lastly, in the NFL, the Cincinnati Bengals and the Chicago Bears don these vibrant colors. It's fascinating to see how these colors are represented across different sports leagues. -
11 May

What is the greatest 'choke' in sports history?
In my opinion, the greatest 'choke' in sports history has to be the 2004 New York Yankees blowing a 3-0 lead in the American League Championship Series against the Boston Red Sox. This collapse was monumental as no team in MLB history had ever come back from a 3-0 deficit to win a best-of-seven series. The Yankees, with their storied history and high expectations, crumbled under the pressure and allowed the Red Sox to make an incredible comeback. This event was not only shocking for baseball fans, but also for the sports world in general, as it demonstrated that even the most dominant teams can fall apart in high-pressure situations. To this day, the 2004 ALCS remains a topic of discussion and a symbol of the unpredictable nature of sports. -
1 May

Will the Kansas City Chiefs be good this year?
As a die-hard football fan, I'm really excited about the upcoming season and can't help but wonder if the Kansas City Chiefs will be good this year. From what I've seen, they're looking strong with their talented roster, including the ever-impressive Patrick Mahomes. The Chiefs' coaching staff has also shown great competence in recent years, which should help keep the team on track. Additionally, their solid draft picks and free agency moves have further bolstered the team's overall potential. So, in my opinion, there's a high chance that the Kansas City Chiefs will indeed be good this year, and I can't wait to see how they perform on the field. -
3 Feb

What is your favorite sports team in California?
My favorite sports team in California is the San Francisco Giants. The Giants have a long and storied history, and they have been one of the most successful teams in Major League Baseball, having won three World Series titles since 2010. I love the team's tradition and their commitment to winning. The Giants have a passionate fan base, and I'm proud to be a part of it. -
2 Feb

Why are there 3 NFL games this Saturday?
This Saturday, January 9th, 2021, three NFL games will be played. This is due to the fact that the NFL has added a seventh playoff seed in each conference, meaning that all four division winners, as well as the three wild card teams, will advance to the playoffs. This has resulted in an additional wild card game being added during the Wild Card Weekend, which takes place on Saturday, January 9th. As a result, three NFL games will be played on this day, giving fans the opportunity to watch three NFL games at the same time.


